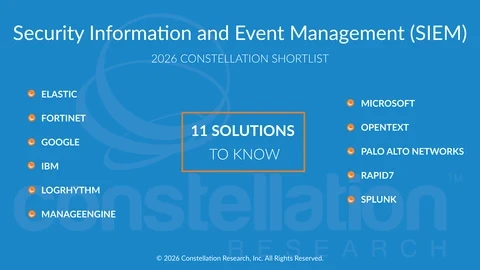
Constellation ShortList™ Security Information and Event Management (SIEM)

Executive Summary
Security Information and Event Management (SIEM) remains a foundational capability for security operations, providing centralized collection, correlation, and analysis of security events across increasingly complex environments. As organizations adopt cloud services, SaaS applications, and identity-centric architectures, SIEM platforms play a critical role in helping security teams investigate incidents, understand attack paths, and maintain operational visibility.
Modern SIEM platforms have evolved beyond log aggregation to support advanced analytics, contextual enrichment, and workflow integration across security operations. Capabilities such as behavioral analysis, threat intelligence correlation, and automated investigation have become table stakes as security teams face growing alert volumes, expanding attack surfaces, and persistent analyst shortages. As a result, SIEM is increasingly positioned as a system of record and decision support layer for security operations, rather than a standalone analytics tool.
At the same time, the SIEM market continues to consolidate, with vendors expanding platform scope through acquisitions and tighter integration with adjacent capabilities such as SOAR, XDR, and cloud security. Buyers are also beginning to explore agentic SOC models, where AI-assisted and agent-based systems support investigation, triage, and response across multiple tools. This shift does not eliminate the need for SIEM, but it does open up alternative architectures where SIEM is complemented, augmented, or, in some cases, partially displaced by broader security analytics and automation platforms. This ShortList reflects both the ongoing relevance of SIEM and the changing ways organizations are evaluating security operations platforms.
Threshold Criteria
Constellation considers the following criteria for these solutions:
Core Capabilities
- Centralized security data ingestion and normalization
Collects, normalizes, and retains security-relevant data from endpoints, networks, cloud services, SaaS applications, identity systems, and security controls.
- Event correlation and security analytics
Correlates events across multiple data sources to identify suspicious activity, attack patterns, and potential security incidents.
- Incident investigation and response workflows
Provides tools and workflows to triage alerts, investigate incidents, and coordinate response actions across security operations teams.
- Contextual enrichment and threat intelligence integration
Integrates threat intelligence and internal context, such as asset criticality and identity data, to improve alert relevance and investigative accuracy.
- Reporting and compliance support
Supports audit, compliance, and regulatory reporting requirements for enterprise security operations.
- Integration and extensibility
Offers open APIs and integrations to connect with endpoint, network, cloud, and response platforms.
Differentiating Capabilities
- Advanced analytics and behavioral detection
Uses behavioral analytics, entity context, and adaptive detection techniques to reduce false positives and surface higher-fidelity alerts.
- Integrated or tightly coupled response automation
Provides native or tightly integrated SOAR capabilities to automate investigation, enrichment, and response workflows.
- Support for agent-assisted security operations
Enables AI-assisted investigation, alert summarization, and guided response in support of emerging agentic SOC models.
- Scalability across hybrid and cloud-native environments
Demonstrates the ability to operate at scale across multi-cloud, hybrid, and high-volume data environments.
-
Platform consolidation and ecosystem alignment
Shows progress toward platform consolidation through native capabilities or deep integration with adjacent security functions such as XDR, SOAR, and cloud security
The Constellation ShortList
Constellation evaluates more than 30 solutions categorized in this market. This Constellation ShortList is determined by client inquiries, partner conversations, customer references, vendor selection projects, market share, and internal research.
Elastic
Fortinet
IBM
LogRhythm
ManageEngine
Microsoft
OpenText
Palo Alto Networks
Rapid7
Splunk
Frequency of Evaluation
Each Constellation ShortList is updated at least once per year. Updates may occur after six months if deemed necessary.
Evaluation Services
Constellation clients can work with the analyst and research team to conduct a more thorough discussion of this Constellation ShortList. Constellation can also provide guidance in vendor selection and contract negotiation.