Transparency and the Future of Work
Transparency and the Future of Work
Transparency is at the heart of modern work and organizations. Tom Malone, in his book, The Future of Work, talks of a shift to more decentralized organizations where there is “participation of people in making the decisions that matter to them” [emphasis in the original]. People can’t make decisions if they don’t have information.
Warren Bennis, in Transparency: How Leaders Create A Culture of Candor, highlights the monetary value of transparency, "[a]gain and again, studies show that companies that rate high in transparency tend to outperform more opaque ones." He cites a 2005 study finding that a group of 27 U.S. companies noted as "most transparent" beat the S&P 500 by 11.3 percent.
Lead By Letting Go: Transparency
I’ve had the chance to talk with a variety of executives about the value of transparency. These conversations, combined with results from peer-reviewed research, prompt me to place transparency at the heart of how you lead by letting go. It’s not that transparency is an absolute positive, but rather that managing transparency is a key skill in our future of work. (Below, I’ve provided links to three articles if you want to follow the recent research on these issues.)
Avinoam Nowogrodski, CEO and founder of Clarizen, the online collaboration and project management company, provides thoughtful advice as well as a tool to support transparency. Over a coffee on the San Francisco waterfront, he and I talked about the challenges of modern work. We are often physically separated from our teammates and the pace of our work seems to be increasing. I’ll add that, though not really a change, it surprises many that the U.S. median tenure with a company is just 4.6 years. We don’t have a lot of face-to-face opportunity to learn from our colleagues.
Technology Can Help
These dynamics are enabled in part by by technology tools. Brynjolfsson and McAfee, in their book, The Second Machine Age, describe the good and the bad of our changing work environment. They suggest that we learn to “race with machines,” rather than against them.
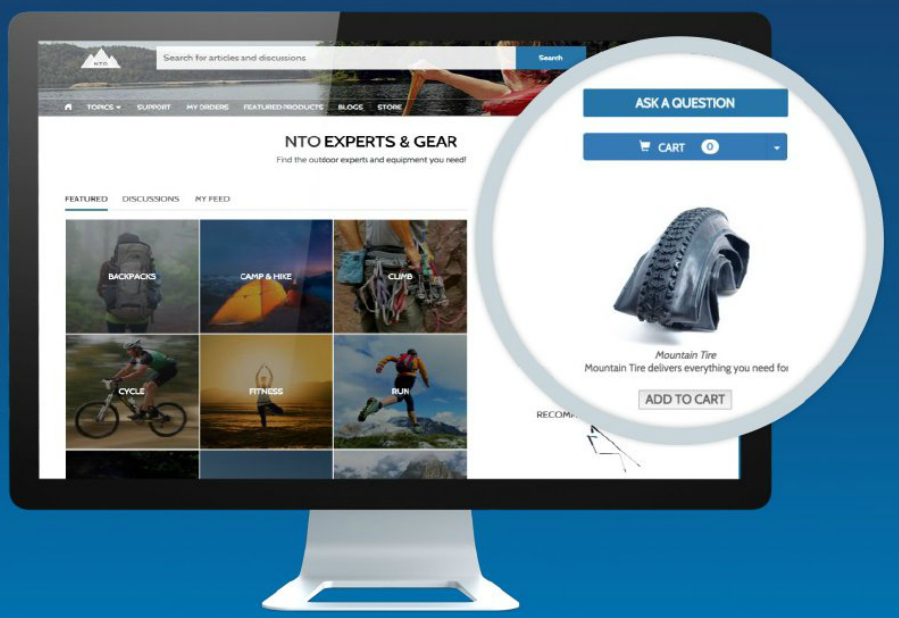
One way the machines can help us is by providing greater transparency around our work. Rather than proactively reporting on our work, the machines can automatically share as we get on with the tasks at hand. Teams do better to the extent that their members know who knows what, who needs what information, and how to coordinate. If we have tools and the will to apply the knowledge gained via the tools, team performance can be supported by technology. In the past, when it was more typical to work in the same room with our teammates, transparency was supported by the technology of the furniture layout. Today, our electronic tools can provide some similar access to knowing who knows, and needs to know, what.
It’s a classic example where the outcome is the result of the human, technical, and organizational dimensions of the work. Transparency has value, if we pay attention to what we see and don’t make the process of providing transparency onerous.
Guiding Principles
Nowogrodski suggests four principles which span the human, technical, and organizational dimensions of work, as well as crossing individual, team, and organizational levels of action:
- Democratic information sharing
- Evolution into a transparent enterprise
- Aligned input and impact
- Organic innovation
It’s not transparency for transparency's sake, but rather for impact and innovation. In an article for Entrepreneur.com, he offers:
[L]eaders within enterprises that exercise transparency do not feel the need to “force feed” transparency to employees. This is because transparency is embedded within the fabric of their culture.They own it. As such, they unleash transparency from within to qualitatively and quantitatively improve employee engagement, workflow management, communication and collaboration, customer support and development, program and project governance, and more.
Take Action -- At the System Level -- Then Let Go
Performance is a combination of motivation, opportunity, and ability. Transparency can help motivation by letting people understand the connection between their actions and their outcomes. Transparency can help opportunity by signaling about the work that needs to be done (I’m looking forward to posting about a recent interview with RallyTeam founder, Dan Ellis, on a related topic). Transparency can help ability as people get feedback closer to their own actions. Build organizational systems that enable transparency, then let people get on with their work. Lead by letting go.
Deep Dives into the Academic Work on Transparency Process and Outcomes
- The Transparency Paradox: A Role for Privacy in Organizational Learning and Operational Control (Bernstein, 2012)
- Organizational Transparency: A New Perspective on Managing Trust in Organization-Stakeholder Relationships (Schnackenberg & Tomlinson, 2014)
- E-leadership: Re-examining transformations in leadership source and transmission (Avolioa, Sosik, Kahai, & Baker, 2014)