Tuesday's Tip: Seven Lessons Learned In Customer Experience Strategies During A Data Breach (such as @Target's)
Tuesday's Tip: Seven Lessons Learned In Customer Experience Strategies During A Data Breach (such as @Target's)
Every Brand Should Have A Plan For A Data Breach
The confluence of centralized personally identifiable information, reliance on digital channels, ease of hacking of magnetic stripes, and the application of the Willy Sutton rule ( a.k.a. you rob banks because that’s where the money is) improve the odds that many organizations will face a data breach. The question is not whether one will happen, but more a question of when and to what extent. How a brand addresses the customer experience component during a data breach will have significant impact that will subsume all other brand efforts up and until the data breach.
Source: Target
On December 19th, Target confirmed reports of a data breach affecting 40 million customers between November 27th and December 15th, 2013. In conversation with over 30 customer experience professionals, many lessons have been learned from the recent Target breach and the largest breach with TJX (TJ Maxx and Marshall’s). The following seven approaches highlight pragmatic and effective strategies to responding and mitigating the damage:
- Begin by isolating and understanding the root cause of the breach. Understanding the root cause enables a realistic understanding of all the options. While it may take some time to get to the source, the investment in resources is worth it. The truth will set you free from weaving an ever growing snow ball of lies and half truths. Saying that you don’t know yet is not good enough. Sharing how you are resolving or approaching the problem helps folks understand the why not the what.
- Catalyze a crisis command center. The command center should not be an after thought but part of the communications readiness training. Prioritize key data. Put all your data sources to work. Identify a protocol for decision making. Quickly agree on talking points and messaging. Democratize decision making and out reach to as many spokes persons as possible. Apply the 9C’s of engagement to build out the crisis journey map. While Target has an excellent social media program, the challenge is tackling crisis communications in defense not offense during the holiday season.
- Trust that transparency is the right course of action. Communicate the breach as early as possible. Do not try to cover it up as Target did. In fact, Target was outed by security expert Brian Krebs first, then Target had to come clean. The result has been disastrous. Get in front of the issue. It’s always easier to proactively influence than react. Customers ultimately value transparency when they can understand the process and the efforts provided to date. Outcomes ultimately matter but in the absence of a solution, upfront communication of the situation and approach helps bridge the trust gap.
- Activate the advocates. Leverage social media to inform key advocates and influencers. Share core messaging. Update frequently. Seek input and advice. Provide the influencers with timely updates and in some cases first line information. While Target has done a good job on Facebook, the issue is not the communications plan, but more that the resolution is not satisfactory.
- Resolve the root cause of the problem. Customers seek resolution, not a patchwork of disparate solutions. In Target’s case, the root cause is a privacy breach on card data. The cleanest way to resolve the situation would be mass card replacement through digital distribution and self service redemption. Target unfortunately chose to use credit card monitoring and put the onus on customers to monitor their fraud status. Customer perceive this as a half-assed measure.
- Make a valuable offer. Use the opportunity to bring back customers not push then away. Provide perceived value. Solicit feedback on potential strategies with brand advocates. Providing a new card with a stored value amount or discount is one approach. Target’s offer of 10% off, coverage for any fraud, and security protection made perfect sense. However, not combining the offer with a brand new card made the offer seem hallow as it did not address the root cause.
- Rebuild trust with subsequent engagement. Determine the next course of actions. Once the crisis has passed, brands must continue to reassure customers on security and privacy. In Target’s case, they will need to announce what measures have been taken, how many folks have been breached, how have folks been compensated, and what is being done in the future to prevent breaches. If the credit card industry is smart, they will also help Target in providing solutions and investing in marketing messages.
The Bottom Line: The Shift To Digital Businesses Require A New Level Of Authenticity
Good leadership is tested in a crisis. The actions any executive has to make during a crisis reflect on the core values of the company. Trust and transparency are key pillars of an authentic business. In a digital world, speed is the other factor that must be considered. Preparing for a crisis is never easy. Preparing for a data breach is actually a bit easier. Why? It’s inevitable and a key requirement in addressing customer experience as we enter a world of digital disruption.
While Monday morning quarterbacking is easy during a crisis, the point here is to take lessons learned from other disasters and get ahead of the issue. One crisis can take down decades and billions of marketing dollars spent building a brand. Handling a crisis well can also remake the image of a brand. A great example is the Tylenol recall of 1982 where the mass drug recall while expensive, proved to reassure the public of J&J McNeil’s sincerity in addressing the root cause.
When product differentiation is not enough and when service differentiation is not enough, all we have our outcomes and experiences. Customer aren’t buying product or services any more. Customers are buying outcomes and experiences. All we have is our brand and how you handle a data breach will determine the future of your organization. How will you prepare to dominate digital disruption?
Your POV.
Are you ready to address customer experience strategies and incorporate digital business transformation in advance of a data breach? Are you embarking on a digital business transformation? Let us know how it’s going! Add your comments to the blog or reach me via email: R (at) ConstellationR (dot) com or R (at) SoftwareInsider (dot) com.
Please let us know if you need help with your Customer Centricity and Digital Business transformation efforts. Here’s how we can assist:
- Assessing customer centricity readiness
- Developing your digital business strategy
- Connecting with other pioneers
- Sharing best practices
- Vendor selection
- Implementation partner selection
- Providing contract negotiations and software licensing support
- Demystifying software licensing
Related Research:
- Tuesday’s Tip: Understand The Five Generation Of Digital Workers
- Monday’s Musings: The Chief Digital Officer In The Age Of Digital Business
- Slide Share: The CMO vs CIO – Pathways To Collaboration
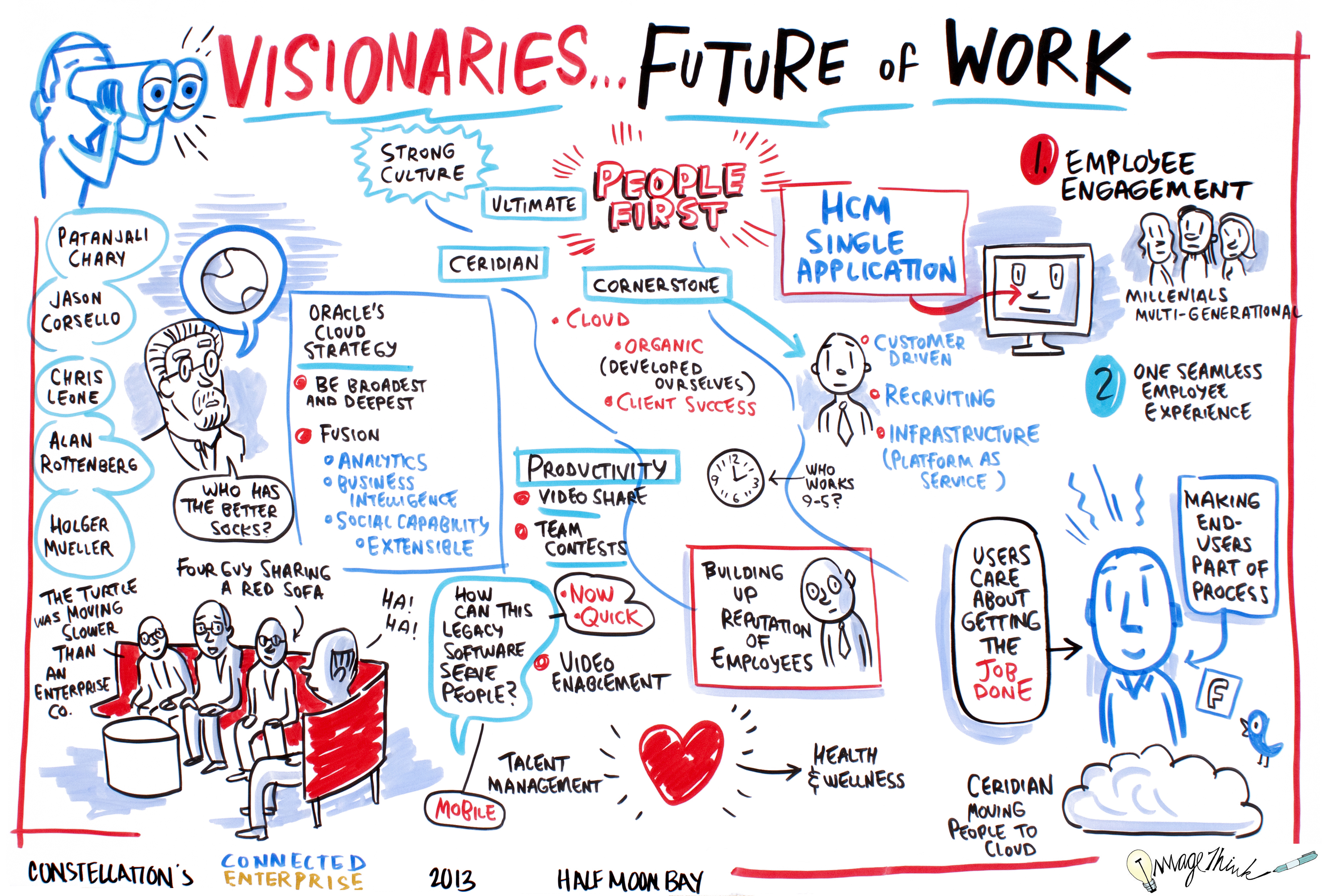
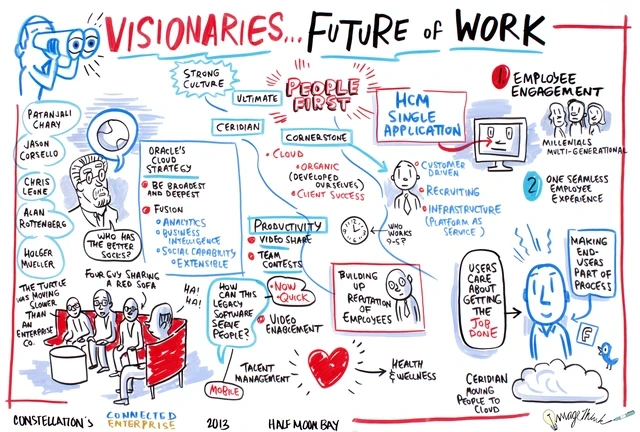
- Event Report: Seven Trends From This Year’s Human Resources Technology Conference 2013 (#HRTechConf)
- Event Report: Metaio’s #InsideAR Conference Hails The Future Of An Always On, Always Augmented Reality
- Event Report: CRM Evolution 2013 – Seven Trends In The Return To Digital Business And Customer Centricity
- Research Summary And Speaker Notes: The Identity Manifesto – Why Identity Is At The Heart of Digital Business
- Monday’s Musings: The Controversy Surrounding Gartner’s CRM Market Share Analysis
- Research Summary: Constellation Cosmos – Cloud Bill of Rights for SaaS Apps, Actian and Netsuite Achieve Epic Status
- Trends: Seven Priorities In The Shift From CMO to Chief Digital Officer
- Monday’s Musings: Understand The Four Organizational Personas Of Disruptive Tech Adoption
- Event Report: The Tweet Stream From #DF12
- Event Report: Dreamforce X (#DF12) Emerges As The South By Southwest (#SXSW) For The Enterprise
- Monday’s Musings: The New Engagement Platform Drives The Shift From Transactions
- News Analysis: KANA Enters MidMarket With Trinicom Acquisition
- Best Practices: From First To Worst – Continental In A Post United World, Lessons In Next Gen Customer Experience
- Monday’s Musings: Seven Basic Privacy Rights Users Should Demand For Social Business
- Monday’s Musings: Balancing The Six S’s In Consumerization Of IT
- Monday’s Musings: A Working Vendor Landscape For Social Business
- Product Review: Google+, Consumerization of IT, and Crossing The Chasm For Enterprise Social Business
- Monday’s Musings: Using MDM To Build A Complete Customer View In A Social Era
- Monday’s Musings: Mastering When and How High End Brands Should Use Daily Deal Sites Such As Groupon
- Best Practices: Applying Social Business Challenges To Social Business Maturity Models
- Research Summary: Software Insider’s Top 25 Posts For 2010
- Best Practices: Five Simple Rules For Social Business
- Research Report: How The Five Pillars Of Consumer Tech Influence Enterprise Innovation
- Research Report: Next Gen B2B and B2C E-Commerce Priorities Reflect Macro Level Trends
- Tuesday’s Tip: Applying The Five Stages Of Adoption Towards SCRM Projects
- Monday’s Musings: Avoiding Failure In Social CRM Projects Requires Ecosystem Coordination
- Research Report: The 18 Use Cases of Social CRM – The New Rules of Relationship Management
- Monday’s Musings: Why Every Social CRM Initiative Needs An MDM Backbone
- Monday’s Musings: 10 Essential Elements For Social Enterprise Apps
Reprints
Reprints can be purchased through Constellation Research, Inc. To request official reprints in PDF format, please contact Sales .
Disclosure
Although we work closely with many mega software vendors, we want you to trust us. For the full disclosure policy, stay tuned for the full client list on the Constellation Research website.
* Not responsible for any factual errors or omissions. However, happy to correct any errors upon email receipt.
Copyright © 2001 – 2013 R Wang and Insider Associates, LLC All rights reserved.
Contact the Sales team to purchase this report on a a la carte basis or join the Constellation Customer Experience!
Marketing Transformation Matrix Commerce New C-Suite Next-Generation Customer Experience Data to Decisions Future of Work Digital Safety, Privacy & Cybersecurity Tech Optimization Innovation & Product-led Growth Revenue & Growth Effectiveness SoftwareInsider Digital Transformation Marketing B2B B2C CX Customer Experience EX Employee Experience AI ML Generative AI Analytics Automation Cloud Disruptive Technology Growth eCommerce Enterprise Software Next Gen Apps Social Customer Service Content Management Collaboration Machine Learning business SaaS PaaS CRM ERP Leadership LLMs Agentic AI HR HCM IaaS Supply Chain Enterprise IT Enterprise Acceleration IoT Blockchain finance M&A Enterprise Service Security Zero Trust Robotics Quantum Computing CCaaS UCaaS developer Metaverse VR Healthcare Chief Customer Officer Chief Executive Officer Chief Marketing Officer Chief Digital Officer Chief Data Officer Chief Experience Officer Chief People Officer Chief Information Officer Chief Technology Officer Chief Analytics Officer Chief Information Security Officer Chief Operating Officer Chief Privacy Officer Chief Revenue Officer Chief Financial Officer Chief Human Resources Officer